Medical City patients may be among the millions nationwide whose personal information is being sold on the dark web. A hacker has claimed responsibility for the HCA data theft that impacted 14 Medical City hospitals and said that the data is now for sale on the dark web. “It has been abundantly clear that HCA do not value client data,” someone representing themselves as the hacker wrote in a forum.
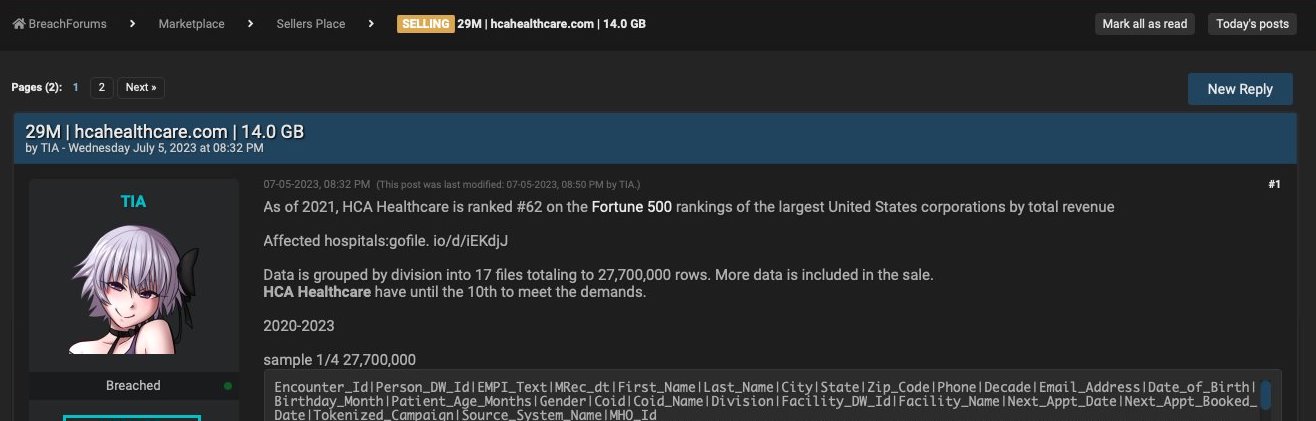
The hacking watchdog site databreaches.net said it has been in contact with someone who claims to be both the hacker and the seller of the HCA data. The site first posted information about the breach on July 5. The seller wrote on a dark web forum that there were more than 27 million records for sale and noted that HCA was ranked 62 on the Fortune 500 list in revenue in 2021.
“Data is grouped by division into 17 files totaling to 27,700,000 rows. More data is included in the sale. HCA Healthcare have until July 10 to meet the demands,” the post says.
The hacker also posted examples of the stolen data, including patients’ names, phone numbers, email, dates of birth, gender, what hospital they visited, and when they visited the facility.
HCA released a statement about the breach describing the stolen data and what the organization thinks wasn’t stolen. The statement said clinical and financial information wasn’t part of the breach. But the hacker told DataBreaches, “I have emails with health diagnosis that correspond to a clientID.” The hacker didn’t provide compelling proof was this case, and HCA told DataBreaches that ClientID does not refer to a particular patient but to the hospital for whom HCA was developing email messaging.
DataBreaches also threw doubts on the number of patients affected, saying it could be more than 11 million given the one million records taken from the San Antonio division alone that the hacker posted on the dark web forum.
Later posts on the same dark web forum show the hacker writing, “It has been abundantly clear that HCA do not value client data…The 27,700,000 lines of data is now for sale.” The forum shows at least two interactions with other users noting that they have messaged the hacker about the data.
Brett Callow, a threat analyst for anti-virus software company Emisoft, tweeted, “This may be one of the biggest healthcare-related breaches of all time.”
The U.S. Health and Human Services Office of Civil Rights said that the nation’s healthcare sector has suffered 295 breaches in the first half of 2023 alone impacting more than 39 million people. In June, Health IT Security compiled a list of the top 10 largest healthcare breaches of the year. The HCA hack is larger than all of them, with the next largest breach impacting nearly 9 million people.
Cybersecurity expert Matthew Yarbrough, who spent years working for the Department of Justice prosecuting cybersecurity criminals before moving into private practice as a partner with the Dallas office of Michelman & Robinson, LLP doing more cybersecurity and data privacy work, says that while the data lost in the HCA hack may seem relatively innocuous, it is still valuable to bad actors.
Name, address, phone, and email information can be used by phishing scammers to get more valuable information, or it can be cross-referenced with information from other data breaches to confirm more sensitive information like social security, driver’s license, or credit card numbers. Additionally, if the stolen information includes the content of the emails sent between doctors or patients, there may be more sensitive and valuable health information. “Until there is more exposure of what the contents of the email are, and if it includes the treatment recommendations or the case analysis. of the patient, that’ll be interesting,” he says. “I can see the damage is much higher.”
Catalyzed by the pandemic, healthcare services continue to move to the cloud, increasing the number of entry points to sensitive data and making health systems more vulnerable to these types of attacks. Yarbrough says they often lack the funding and expertise to deploy the right technology to repel a sophisticated attack. Because of HIPAA, healthcare organizations are held to a higher standard in protecting data. As a result, Health and Human Services could levy fines and penalties on HCA for not keeping the data secure. In some states, patients may be able to sue HCA directly for not securing their data (but not in Texas). “You’re only going to continue to see Texas hospitals attacked by these sorts of groups, but it’ll also apply to municipalities and Texas companies as well.”
So is HCA likely to meet the hacker’s demands before it is sold on the dark web? HCA hasn’t said one way or the other, but Yarbrough says the hackers are often international and not extraditable, meaning law enforcement can do little to help the organizations whose data was stolen. As ransomware and data breaches have become more common, cyber insurance has become prohibitively expensive for many organizations, meaning that meeting hackers’ demands is often the best option. The ransom is often paid with cryptocurrency, as it was with the Dallas County Appraisal District earlier this year, making the thief even more challenging to catch.
Prevention, Yarbrough says, is the best way to deal with would be hackers and data breaches, especially as attackers become more sophisticated, more sensitive data is stored on external servers, and people continue to work and live remotely.
“The best advice I can give to companies or hospitals is to one, work on your incident response plans. Two, start working on your training, and three, build out robust prevention processes and procedures and train and assess those on an annual basis,” Yarbrough says. “It’s not going away, especially now that it has been monetized as a service.”
Author